Live Panel Interviews With Evidence Packs, Not Privacy Debt
A compliance-first operating model for panel interviews: identity gate access, instrument every decision, and retain only what you can defend.
If it is not logged, it is not defensible. Design the panel interview like privileged access: identity gate, consent gate, and evidence pack.Back to all posts
## 1) HOOK: Real Hiring Problem
A remote engineering panel ends with a "no hire" and a candidate dispute. Legal asks two questions you cannot answer quickly: who actually attended the interview, and what evidence supports the decision. If your artifacts are scattered across a video tool, a shared drive, and free-text notes, you have a defensibility failure. The operational impact is predictable: the offer pipeline slows while Compliance reconstructs evidence, SLAs slip, and hiring managers start bypassing controls to keep throughput. Fraud pressure compounds it. Industry reporting frames hiring as a security surface area. Pindrop observed that 1 in 6 applicants to remote roles showed signs of fraud in one real-world pipeline, which means your panel workflow is not only an HR process. It is an identity and access problem with privacy consequences if you over-collect or retain uncontrolled recordings. Cost is not hypothetical. Mis-hire replacement costs are often estimated at 50-200% of annual salary depending on role and context. In a compliance seat, the hidden cost is the rework: escalations, legal review time, and audit exposure when you cannot produce a complete, time-stamped decision record.
Legal exposure: inconsistent consent, uncontrolled transcripts, and unverifiable attendance undermine defensibility.
Audit readiness: if you cannot retrieve who scored what, when, and based on which rubric, the decision is not audit-ready.
Speed and cost: delays cluster where identity is unverified and where evidence must be reconstructed under time pressure.
## 2) WHY LEGACY TOOLS FAIL
Legacy interview stacks were assembled to schedule conversations, not to produce audit-grade evidence. The market failure is structural: ATSs store stages but not proof, interview tools store recordings but not hiring context, and assessment tools store scores but not reviewer rationale. Operationally, most teams still run sequential checks that create a slow waterfall: schedule first, verify later, record ad hoc, then chase scorecards during debrief. That sequencing causes two outcomes: time-to-offer expands, and reviewers create shadow workflows to compensate. The compliance gap is consistent across tools: no unified evidence pack, weak or missing immutable event logs, and no review-bound SLAs for scorecard completion, consent capture, transcript access, or exception handling. When the artifacts live in different systems, "who approved this candidate" becomes a multi-hour reconstruction exercise with unclear accountability.
Time from panel end to last scorecard submitted (reviewer latency).
Number of recording links shared outside approved roles (access sprawl).
Time from candidate dispute to evidence pack retrieval (defensibility latency).
## 3) OWNERSHIP & ACCOUNTABILITY MATRIX
Assigning ownership is the difference between a controlled workflow and a collection of tools. The rule: Recruiting Ops owns workflow integrity, Security owns access control and audit policy, and Hiring Managers own rubric discipline and timely scoring. Define what is automated vs manually reviewed. Automation should handle identity gating, consent capture prompts, rubric enforcement, evidence pack assembly, and SLA timers. Manual review should be reserved for exceptions: verification failures, suspected proxy signals, or consent denials. Set sources of truth explicitly. The ATS should be the system of record for stage and disposition. The interview evidence pack should be ATS-anchored and tamper-resistant, with immutable links to interview artifacts and event logs. Identity verification should be authoritative for candidate presence, not a checkbox in notes.
Recruiting Ops: panel template, rubric versioning, SLA configuration, debrief workflow.
Security: identity gate policy, role-based access, retention windows, export controls, audit log requirements.
Hiring Manager: scorecard criteria, required rationale fields, reviewer accountability for on-time submission.
Legal/Privacy: consent language, regional recording rules, data minimization and retention approval.
Analytics: time-to-event dashboards and segmentation by role, location, risk tier.
## 4) MODERN OPERATING MODEL
Design the panel as an instrumented workflow, not a meeting. The recommendation is simple: gate access by verified identity, capture consent as a logged event, and generate an evidence pack that ties attendance, questions, scoring, and artifacts to one candidate record. Start with identity verification before access. Do not let a join link become a bearer token. Issue join credentials only after liveness, face match, and document authentication pass for the scheduled candidate, with step-up verification when risk signals appear. Run event-based triggers. When the candidate passes identity, the system schedules and issues access. When the meeting starts, it logs attendance and starts recording only after consent is captured. When the meeting ends, it opens a review-bound SLA for scorecards and locks rubric criteria to prevent post-hoc edits. Automate evidence capture and minimize privacy exposure at the same time. Store structured scorecards and required rationale fields as the primary decision evidence. Treat recordings and transcripts as controlled supplements, not the default source of truth. Use role-based access, access expiration by default, and retention windows approved by Legal. Measure with dashboards built on timestamps: time-to-verify, time-to-interview, time-to-scorecard completion, and time-to-debrief decision. Compliance can then pinpoint where delays cluster and where access sprawl is occurring.
Consent as a discrete, time-stamped event required to start recording and transcription.
Data minimization: structured scorecards first, recordings only when justified by policy.
Access expiration by default for recordings and transcripts, with logged exceptions.
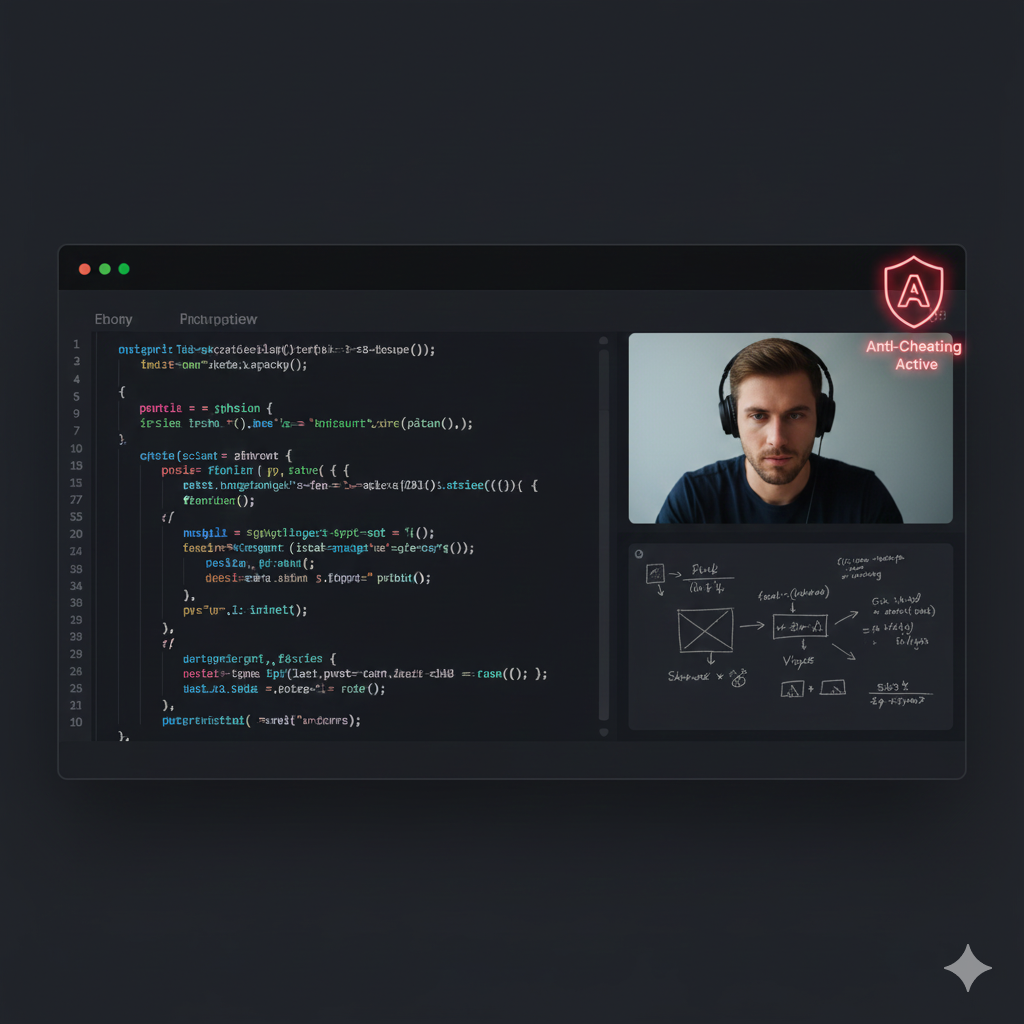
## 5) WHERE INTEGRITYLENS FITS
IntegrityLens AI acts as the ATS-anchored control plane for interviews and evidence handling, so Compliance gets one defensible record per candidate instead of scattered artifacts. - Identity gate before access using biometric verification (liveness, face match, document auth) with under-three-minute typical verification time, logged as immutable events. - Fraud prevention signals (deepfake detection, proxy interview detection, behavioral signals) routed into a review-bound queue with explicit SLAs and reviewer accountability. - Integrated ATS lifecycle management that ties interview scheduling, panel membership, and disposition to a single candidate identity and audit trail. - AI screening interviews and technical assessments, including coding assessments across 40+ languages with plagiarism detection and execution telemetry, writing evidence back to the candidate record. - Evidence packs with time-stamped scorecards, structured notes, recording and transcript references, and tamper-resistant logs that answer Legal's "who approved what, when, and based on what" question.
From: recordings everywhere, unclear retention, unclear access.
To: evidence-by-design, minimal retention, access controls, and retrieval in minutes.
## 6) ANTI-PATTERNS THAT MAKE FRAUD WORSE
- Sharing static join links before identity verification, which turns "attendance" into an unverified bearer token and enables proxy candidates. - Recording by default with no logged consent event, then circulating transcripts in email or chat, creating uncontrolled copies and unclear legal basis. - Allowing free-text scorecards and post-hoc rubric edits, which produces non-comparable feedback and weakens audit defensibility when decisions are challenged.
They break chain-of-custody for who was evaluated.
They create retention sprawl you cannot confidently delete or justify.
They increase debrief ambiguity and bias because evidence is not standardized.
## 7) IMPLEMENTATION RUNBOOK
Define the panel template and rubric version Owner: Hiring Manager (rubric), Recruiting Ops (template). SLA: 2 business days per role family update. Logged: rubric_id, criteria, version, approver, timestamp. #
Configure consent and retention policy by region and role risk tier Owner: Legal/Privacy (policy), Security (controls). SLA: 5 business days for initial approval, 24 hours for updates triggered by regulation changes. Logged: policy_id, lawful basis, consent text hash, retention_days, access roles. #
Identity gate before issuing candidate access Owner: Security (policy), Recruiting Ops (execution monitoring). SLA: verification completed at least 30 minutes before panel start; exceptions resolved within 15 minutes. Logged: document auth result, liveness result, face match result, reviewer actions, timestamps. #
Start the session with attendance logging and consent gating Owner: Recruiting Ops. SLA: consent captured before recording starts; if consent denied, recording disabled and scorecard-only mode enforced. Logged: attendance, consent event, recording start/stop timestamps. #
Structured note-taking and scorecards during the panel Owner: Hiring Manager (enforcement), interviewers (completion). SLA: scorecards due within 2 hours of panel end. Logged: per-interviewer scorecard submission time, criterion scores, required rationale fields, tamper-resistant edits. #
Debrief with evidence-based scoring only Owner: Hiring Manager. SLA: debrief within 24 hours; decision logged within 1 hour post-debrief. Logged: decision, decision owner, evidence pack reference, dissent notes if applicable. #
Exception handling for fraud or privacy escalations Owner: Security (fraud), Legal/Privacy (privacy). SLA: high-risk queue triage in 30 minutes during business hours, 4 hours after hours; documented disposition required. Logged: risk signal, reviewer, actions taken, outcome, access changes. #
Evidence pack finalization and access expiration Owner: Recruiting Ops (pack assembly), Security (access). SLA: pack available within 15 minutes after decision; recording/transcript access auto-expires per policy. Logged: evidence_pack_id, artifact pointers, access grants, exports, deletions, retention timers.
## 8) SOURCES
All numeric claims in this briefing are sourced from the links above or from IntegrityLens approved proof points.
## 9) CLOSE: IMPLEMENTATION CHECKLIST
If you want to implement this tomorrow, start by instrumenting the panel like an access workflow and forcing standardization where disputes typically occur. - Enforce identity gate before access for every panel candidate, with a documented exception path and SLA-bound review queue. - Make consent a required, logged event before any recording or transcription starts, and define "scorecard-only mode" when consent is denied. - Standardize rubrics and lock versions per role family. Require rationale fields and prohibit post-hoc rubric edits. - Set review-bound SLAs: scorecards due within 2 hours, debrief within 24 hours, decision logged within 1 hour after debrief. - Generate an ATS-anchored evidence pack per candidate with immutable event logs: identity results, attendance, consent, scorecards, and artifact pointers. - Reduce privacy exposure: role-based access to recordings/transcripts, access expiration by default, retention timers, and export logging. Business outcomes you should see when this is working: reduced time-to-hire (fewer debrief rehashes), defensible decisions (retrievable evidence packs), lower fraud exposure (identity-gated access), and standardized scoring across teams (comparable rubrics and timestamps).
Evidence pack retrieval time measured in minutes, not hours.
Scorecard SLA compliance above your internal target, segmented by function.
Zero uncontrolled exports of transcripts or recordings without a logged exception.
Related Resources
Key takeaways
- Treat the live panel as a privileged-access event: identity gate before join, explicit consent before record, and access expiration by default.
- Audit readiness comes from an ATS-anchored evidence pack: time-stamped scorecards, notes, and recording/transcript references tied to a single candidate identity.
- Privacy risk is reduced by policy: role-based access, review-bound SLAs, minimal retention windows, and documented exception handling.
- Debrief time drops when rubrics are standardized and tamper-resistant, and when every reviewer has accountable timestamps, not narrative recollection.
A policy template that enforces identity gating, consent-based recording, role-based access, retention windows, and immutable event logging for live panel interviews.
version: 1
policy_id: panel-interview-evidence-privacy
scope:
workflow: live_panel_interview
applies_to: [scorecards, notes, recordings, transcripts]
identity_gate:
required_before_access: true
methods:
- document_auth
- liveness
- face_match
step_up_verification:
enabled: true
triggers:
- proxy_interview_signal
- deepfake_signal
- device_anomaly
sla:
verify_by_minutes_before_interview: 30
exception_review_minutes: 15
consent:
recording_requires_consent: true
transcript_requires_consent: true
consent_capture:
method: explicit_clickthrough
store:
event_log_only: true
fields: [candidate_id, session_id, consent_version, timestamp]
if_consent_denied:
recording: disabled
transcript: disabled
mode: scorecard_only
recording_and_transcript_controls:
access_model:
roles_allowed:
recordings: [recruiting_ops, hiring_manager, legal_privacy]
transcripts: [recruiting_ops, hiring_manager, legal_privacy]
access_expiration_hours: 72
export:
allowed: false
exception_path:
requires_approval_roles: [legal_privacy]
log_export_event: true
retention:
default_days: 30
risk_tiers:
low: 14
medium: 30
high: 90
zero_retention_biometrics: true
scorecards_and_notes:
rubric_version_required: true
required_fields: [criterion_scores, rationale, recommendation]
submission_sla_hours_after_interview: 2
edit_policy:
allow_edits_until_sla_deadline: true
after_deadline: locked
immutable_event_log:
required: true
events:
- identity_verification_completed
- interview_access_issued
- session_attendance_logged
- consent_captured
- recording_started
- recording_stopped
- transcript_generated
- scorecard_submitted
- debrief_decision_logged
- evidence_pack_finalized
- artifact_viewed
- artifact_access_granted
- artifact_access_revoked
- retention_timer_started
- retention_deletion_executed
review_queues:
fraud_signals:
owner: security
sla_minutes_business_hours: 30
sla_minutes_after_hours: 240
privacy_exceptions:
owner: legal_privacy
sla_hours: 24
sources_of_truth:
candidate_record: ats
evidence_pack_index: ats
identity_results: integritylens
audit_log: integritylensOutcome proof: What changes
Before
Panel interviews produced scattered artifacts: recordings in the video tool, scorecards in documents, and consent handled inconsistently. Candidate disputes triggered manual evidence reconstruction and access sprawl across teams.
After
Panels were converted into an instrumented workflow: identity gate before access, consent-gated recording, standardized rubrics, and ATS-anchored evidence packs with immutable event logs and access expiration.
Implementation checklist
- Define what gets recorded vs not recorded, and why, before enabling transcripts.
- Require identity verification before issuing a join link to any candidate.
- Use standardized scorecards with locked criteria and required rationale fields.
- Enforce review SLAs for scorecard submission and exception queues.
- Restrict access to recordings/transcripts by role and auto-expire access.
- Set retention by risk tier and legal basis, and log every export/view event.
Questions we hear from teams
- What should be the primary evidence for a panel decision if we want to reduce privacy risk?
- Use structured scorecards with required rationale fields as the primary decision evidence. Treat recordings and transcripts as supplementary artifacts that require consent, role-based access, and short retention windows.
- How do we stay audit-ready if a candidate refuses recording?
- Enforce a scorecard-only mode: log attendance, log the consent denial event, require standardized scorecards, and finalize an evidence pack that references the rubric version and reviewer submissions.
- How do you prevent link-sharing and proxy candidates in live panels?
- Do not issue join access until identity verification is complete, and log the identity verification event with timestamps. Add step-up verification when proxy or deepfake risk signals are detected.
- What retention window is defensible for interview recordings and transcripts?
- Set a default short window approved by Legal and vary it by risk tier and jurisdiction. The defensible posture is not a universal number, but that retention is policy-driven, time-bound, and deletion is logged.
Ready to secure your hiring pipeline?
Let IntegrityLens help you verify identity, stop proxy interviews, and standardize screening from first touch to final offer.
Watch IntegrityLens in action
See how IntegrityLens verifies identity, detects proxy interviewing, and standardizes screening with AI interviews and coding assessments.
