Blind Code Reviews Without Blind Spots: An Ops Runbook
A practical operating model for running anonymous work-sample scoring while keeping identity risk, audit defensibility, and time-to-offer under control.
Blind reviews only reduce bias if you do not create a new anonymous access path. Gate access on identity, then anonymize scoring, and log every decision as evidence.Back to all posts
Real Hiring Problem
Blind-review programs fail when anonymity is implemented without identity gating and timestamps. The common incident is link issuance before verification, followed by unprovable scoring changes and exception approvals. Replacement cost exposure can run 50-200% of annual salary for a mis-hire, turning process gaps into budget risk.
Audit liability when approvals and score edits are not attributable
Legal defensibility gaps when you cannot prove the blind-review policy was followed
SLA breakdown when identity is verified late and interviews must be rescheduled
Why legacy tools fail
Legacy ATS, background checks, and assessment tools were built as single-step utilities, not as an instrumented workflow. They create sequential checks, siloed evidence, and spreadsheet-based rubrics that cannot be audited. The result is shadow workflows where exceptions live outside the system of record.
No unified evidence pack tied to a submission ID
No immutable event log across identity, scoring, and approvals
No review-bound SLAs for scoring and overrides
Ownership and accountability matrix
Assign owners by control surface: Recruiting Ops owns workflow and SLAs, Security owns access control and audit policy, Hiring Managers own rubric discipline and scoring. Define systems of record explicitly so disputes do not devolve into email archaeology.
ATS: stage transitions and final decision record
Verification service: identity events and step-up outcomes
Assessment system: artifacts, telemetry, and plagiarism signals
Modern operating model
Run blind reviews as two coupled lanes: identity gating for access, and anonymized scoring for evaluation. Use event-based triggers to issue access, assign reviewers, enforce SLAs, and assemble evidence packs automatically.
Identity gate before access
Versioned rubrics with required evidence-based notes
Segmented risk dashboards that track time-to-event and integrity flags together
Where IntegrityLens fits
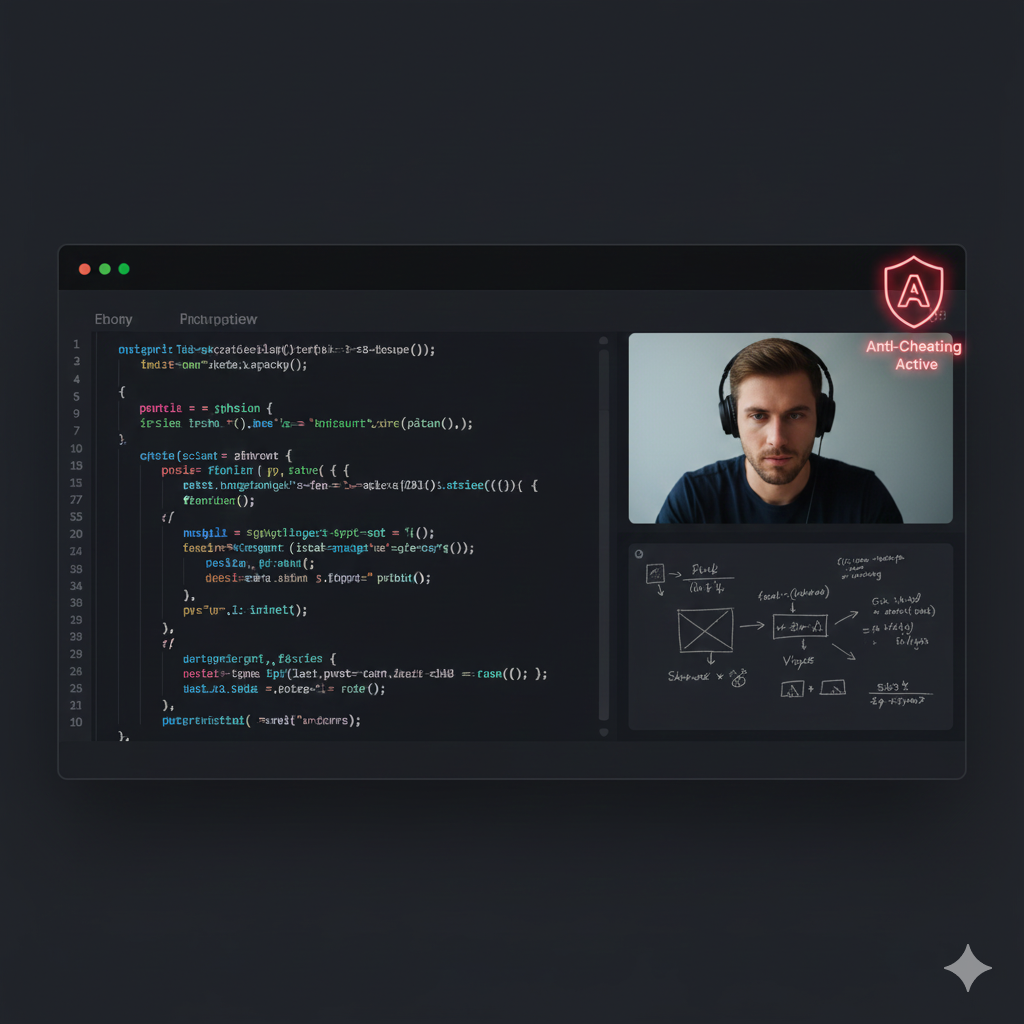
IntegrityLens enables anonymized scoring without giving up access control, audit trails, or SLA enforcement. It gates assessment access on verification, captures integrity signals as evidence, and writes workflow outcomes back to the ATS as the single source of truth.
Identity verification in under three minutes before assessment access is granted
AI coding assessments across 40+ languages with plagiarism detection and execution telemetry for evidence packs
Configurable SLAs and event-based triggers for reviewer assignment and escalations
ATS write-backs to avoid shadow workflows
Immutable evidence packs and compliance-ready audit trails
Anti-patterns that make fraud worse
Do not implement blind reviews in ways that create new unlogged access paths or unreviewable exceptions.
Blind access: anonymize reviewers but issue links before identity gating
Off-platform rubrics: score in spreadsheets or chat, then copy results into the ATS
Unlogged overrides: allow outcome changes without justification, approver, and timestamp
Implementation runbook
Implement blind reviews by sequencing controls, owners, SLAs, and evidence requirements per stage. Operate it like access management: no access without identity, no decisions without evidence, no exceptions without logged approvals.
Define blind boundary (Owner: Recruiting Ops, SLA: 2 business days, Log: policy version and exceptions)
Lock rubric and prompt versions (Owner: Hiring Manager with Recruiting Ops enforcement, SLA: 3 business days, Log: rubric ID and approver)
Identity gate before token issuance (Owner: Security policy, Recruiting Ops execution, SLA: 10 minutes, Log: verification events)
Anonymous submission capture (Owner: Recruiting Ops, SLA: 72 hours, Log: token issuance, start, submission, telemetry refs)
Review-bound scoring queue (Owner: Hiring Manager, SLA: 24 hours, Log: reviewer assignment, score, rubric items, notes)
Step-up verification on risk triggers (Owner: Security, SLA: 4 hours, Log: trigger reason and outcome)
Debrief via evidence pack (Owner: Hiring Manager, SLA: 30 minutes meeting, Log: decision and override rationale)
ATS write-back and retention enforcement (Owner: Recruiting Ops and Security, SLA: same day, Log: stage change and retention policy ID)
Sources
Checkr: Hiring Hoax (Manager Survey, 2025) https://checkr.com/resources/articles/hiring-hoax-manager-survey-2025 SHRM: replacement cost estimates https://www.shrm.org/in/topics-tools/news/blogs/why-ignoring-exit-data-is-costing-you-talent
31% false-identity interview exposure (manager-reported)
50-200% salary replacement cost range
Close: Implementation checklist
Start with access control and evidence, then add anonymity as a reviewer-visibility rule. If you cannot retrieve who approved a candidate and what evidence they used, your process is not audit-ready.
Gate assessment access on verification with a 10-minute SLA and a manual review queue
Use anonymized submission IDs and forbid resubmission without a new ID
Lock rubrics and require per-item evidence-based notes
Run scoring in a review-bound SLA queue with escalation
Log overrides with justification and second approval
Write evidence pack pointers into the ATS record for every decision
Related Resources
Key takeaways
- Blind reviews are a scoring control, not a fraud control. You need an identity gate before any privileged access to assessment links.
- The minimum viable blind-review system has three artifacts: an anonymized submission ID, a locked rubric, and an immutable event log tying score changes to a reviewer and timestamp.
- Speed comes from parallelized checks: run anonymized scoring while identity verification runs in a review-bound SLA queue.
- Audit readiness requires evidence packs that can answer: who scored, on what rubric, using which artifacts, and when approvals happened.
- Interviewer defense improves when reviewers only see what they need: the work, the rubric, and integrity signals. Not the candidate profile.
Use this policy artifact to define where anonymity applies, which events must be logged, and which SLAs are enforced.
Recruiting Ops owns the workflow fields, Security owns the identity gate controls, and Hiring Managers own rubric compliance and override discipline.
blind_review_policy:
policy_id: "blind-review-v1"
objective: "Anonymous scoring with identity-gated access and audit-ready evidence."
stages:
- name: "identity-gate"
owner: "Security"
sla_minutes: 10
required_events:
- "verification.started"
- "verification.passed"
controls:
- "no assessment token until verification.passed"
- "manual review queue if verification.inconclusive"
- name: "assessment-access"
owner: "RecruitingOps"
sla_minutes: 5
required_events:
- "assessment.token_issued"
controls:
- "token TTL hours: 72"
- "one token per candidate per attempt"
- name: "anonymous-scoring"
owner: "HiringManager"
sla_hours: 24
reviewer_visibility:
allowed_fields:
- "submission_id"
- "prompt_version"
- "rubric_version"
- "code_artifacts"
- "execution_telemetry"
- "plagiarism_signals"
blocked_fields:
- "candidate_name"
- "photo_or_video"
- "resume"
required_events:
- "reviewer.assigned"
- "score.submitted"
required_fields:
- "rubric_item_scores"
- "evidence_based_notes"
- name: "override"
owner: "HiringManager"
sla_hours: 4
controls:
- "requires written justification"
- "requires second approver: RecruitingOps"
required_events:
- "override.requested"
- "override.approved"
audit:
log_format: "immutable_event_log"
evidence_pack:
must_include:
- "rubric_snapshot"
- "prompt_snapshot"
- "telemetry_refs"
- "plagiarism_refs"
- "review_notes"
- "approval_chain"
retention:
biometrics: "zero-retention where policy permits"
evidence_pack_days: 365
Outcome proof: What changes
Before
Anonymous scoring was attempted by manually stripping candidate identifiers, but assessment links were issued before identity verification and scoring notes lived in spreadsheets. When exceptions occurred, approvals were not attributable and debriefs required re-reviewing artifacts.
After
Assessment access was gated on identity verification, scoring was performed on submission IDs with locked rubrics, and every score, override, and approval produced an ATS-anchored evidence pack with timestamps.
Implementation checklist
- Define which stages are blind and which are identity-gated
- Assign owners for SLAs, overrides, and audit policy
- Lock rubrics and require evidence-based scoring comments
- Create anonymized submission IDs and forbid resubmission without a new ID
- Instrument event logs for link issuance, starts, submissions, reviews, overrides, and final approvals
- Implement step-up verification for high-risk signals before any live interview
Questions we hear from teams
- What is a blind review in hiring?
- A blind review is a scoring stage where reviewers evaluate a work sample using a fixed rubric without seeing candidate identifiers such as name, photo, or resume. It is a scoring control that must be paired with identity gating to avoid creating an anonymous access path.
- Do blind reviews reduce hiring fraud?
- Not by themselves. Blind reviews can increase fraud risk if assessment access is granted before identity verification. Fraud reduction comes from identity gating before access, step-up verification on risk signals, and immutable logs tying submissions and scores to accountable reviewers.
- What evidence do we need for audit-ready blind reviews?
- At minimum: a submission ID, rubric and prompt snapshots, reviewer assignment and scoring timestamps, reviewer notes tied to rubric items, integrity signals (for example plagiarism indicators and execution telemetry), and an approval chain for overrides. The evidence must be retrievable from the ATS record.
- How do we keep blind reviews fast?
- Parallelize checks instead of running a waterfall. Run identity verification in a short SLA queue before access, then trigger anonymous scoring immediately on submission with a 24-hour reviewer SLA and escalation rules. Measure time-to-event at each checkpoint rather than relying on averages.
Ready to secure your hiring pipeline?
Let IntegrityLens help you verify identity, stop proxy interviews, and standardize screening from first touch to final offer.
Watch IntegrityLens in action
See how IntegrityLens verifies identity, detects proxy interviewing, and standardizes screening with AI interviews and coding assessments.
