False Positives Playbook: Clearing Honest Candidates Fast
A support-first, audit-ready process for when a real candidate gets flagged and your team has to act fast without burning trust.

A fraud flag is a routing decision, not a verdict. Your job is to clear the honest candidate quickly while preserving evidence good enough for an audit and calm enough for Support.Back to all posts
When an honest candidate triggers a fraud flag
Assume it is 4:45 PM Friday. A candidate in a late-stage coding assessment gets flagged for "anomalous environment," their score is quarantined, and the recruiter forwards your Support inbox a one-line ask: "Can you clear them today?" The candidate replies-all with legal-sounding language, the hiring manager threatens to "just use a different tool," and your team has no consistent script. The operational goal is not to argue with the candidate or override the system. The goal is to resolve the status in the ATS with defensible evidence and a documented decision path so the pipeline keeps moving and your brand does not take damage.
Why false positives hit Support harder than Security
False positives create high-cost work because the "customer" is emotional and time-sensitive: candidates, recruiters, and hiring managers all want an immediate answer. Every extra hour increases the chance of social escalation, candidate withdrawal, or shadow decisions like bypassing controls. Checkr reports that 31% of hiring managers say they have interviewed someone who later turned out to be using a false identity. Directionally, that implies integrity controls are justified and leadership will keep adding them. It does not prove your org has the same base rate, nor does it justify treating every flag as fraud without review. Pindrop reports that 1 in 6 applicants to remote roles showed signs of fraud in one real-world pipeline. Directionally, that suggests remote hiring produces enough suspicious signals to require triage. It does not mean 1 in 6 are confirmed fraud, and it definitely does not tell you the false-positive rate of any single vendor or model.
Ticket volume from "I was accused" complaints
Time-to-clear and time-in-queue for manual review
Re-open rates when decisions are not explained with evidence
Recruiter workarounds that create audit findings
Ownership, automation, and sources of truth
Recommendation: define ownership as a RACI and publish it internally. False positives become chaotic when Support is implicitly making hiring decisions. Ownership model that works in practice: Recruiting Ops owns the policy and thresholds, Security owns high-risk escalations and exception controls, Hiring Managers own hire/no-hire based on job signal, and Support owns candidate communication, SLA tracking, and evidence collection quality. Automated vs manual: automation should do first-pass routing (auto-clear, step-up, queue). Manual review should only happen when the flag meets explicit criteria and the review packet is complete. Sources of truth: the ATS is the canonical state machine (status, timestamps, decisions). The verification service is the identity evidence system (doc match, liveness, biometric result). The interview and assessment systems are the performance evidence systems (transcripts, recordings, telemetry). Support should not maintain "shadow truth" in email threads.
Recruiting Ops: owns flag policy, queue rules, and training for reviewers
Security: owns step-up controls for high-risk cases and fraud pattern investigation
Support/CS: owns candidate comms templates, appeal intake, and SLA adherence
TA leaders: approve policy changes that affect funnel speed or candidate experience
A practical policy for treating flags as signals, not verdicts
Recommendation: require two independent signals before any adverse action, and create a fast "clear lane" for common benign causes. Most false-positive blowups happen when a single weak signal triggers a hard stop. Your policy should separate: (1) integrity-of-person (is this the same human), (2) integrity-of-session (is the session manipulated), and (3) integrity-of-output (does the work product match the expected constraints). Use Risk-Tiered Verification: start with low-friction checks, then step up only when the combination of signals justifies it. The policy should also include de-escalation criteria so honest candidates do not get stuck in review queues.
Identity checks pass (document + face + voice where applicable) and the flag is only environment-related (VPN, IP change, travel)
Assessment telemetry shows normal interaction patterns and no prohibited tool usage signals
Candidate provides a consistent, plausible explanation that matches timestamps (hotel Wi-Fi, shared workspace, accessibility software)
Identity mismatch or liveness uncertainty combined with assessment anomalies
Multiple candidates share device fingerprints or repeated environment signatures
Refusal to complete a low-friction step-up after clear explanation of purpose
Triage policy artifact you can actually run
Use this as a starting point for your queue routing rules. It is designed for Support-led intake with Recruiting Ops ownership and Security escalation for high-risk cases.
Step-by-step: clear the honest candidate without breaking the pipeline
Freeze the right thing, not everything. Quarantine the single assessment attempt or interview session, not the entire candidate record. Keep scheduling moving while you review, unless the risk is identity-of-person.
Build the Evidence Pack before you answer anyone. Pull verification result, liveness outcome, doc match confidence, device and network signals, and assessment telemetry. Add a short timeline: when the flag occurred, what changed, what the system observed.
Classify the flag into one of three buckets: benign environment, ambiguous integrity-of-session, or high-risk identity-of-person. This prevents "reviewer vibe" decisions.
Run the lightest step-up first. Example: re-run a 2-3 minute verification check before the next live interaction, or require a short "explain your approach" async prompt tied to the assessment submission. Do not add friction unrelated to the suspected vector.
Decide with documented criteria. If cleared, record the clearance reason code. If stepped up, record what step-up was requested and the deadline. If denied, require dual sign-off (Recruiting Ops + Security) and attach the Evidence Pack.
Communicate like Support, not like a compliance bot. Tell the candidate what happened in plain language, what data you used, what you need next (if anything), and how to appeal.
Close the loop in the ATS. Update status, tag the outcome, and ensure the hiring team sees "cleared" or "step-up requested" instead of a raw fraud label.
Never say "you cheated" based on a flag. Say "we detected an inconsistency and need to confirm X."
Give a time-bound next step and a human point of contact for accessibility or special circumstances.
Explain what you retain and for how long in general terms, and point to the consent language they accepted.
Anti-patterns that make fraud worse
- Zero-tolerance auto-reject on a single signal, which trains fraudsters to probe your thresholds and punishes honest edge cases. - Letting recruiters "override" via side channels, which creates an audit gap and makes your controls socially gameable. - Asking for excessive personal data during appeal, which increases privacy risk and makes candidates less cooperative.

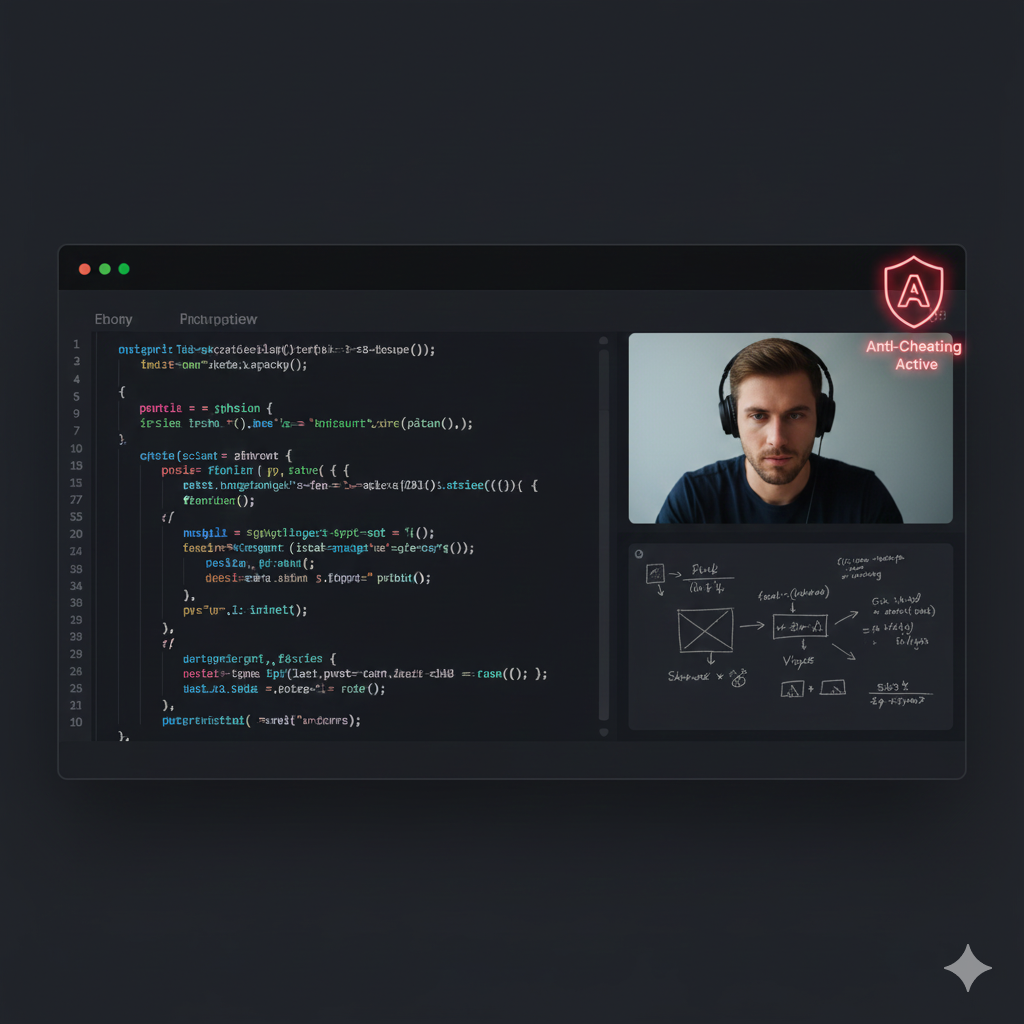
Where IntegrityLens fits
IntegrityLens AI is built for this exact operator problem: keeping hiring moving while you can defend every integrity decision. It combines ATS workflow, biometric identity verification, fraud detection, AI screening interviews, and coding assessments in one pipeline so flags do not scatter across tools. Teams use Risk-Tiered Verification to step up only when signals justify it, Evidence Packs to standardize what reviewers see, and Zero-Retention Biometrics patterns to reduce privacy exposure. TA leaders and Recruiting Ops run the funnel, CISOs get defensible controls, and Support gets a consistent appeal and resolution workflow instead of ad hoc escalations.
ATS status changes tied to immutable verification and assessment events
Queue routing rules for auto-clear, step-up, and manual review
Evidence Pack generation for disputes and audit responses
Idempotent Webhooks to keep downstream systems consistent
What to measure so false positives do not become chronic
Recommendation: treat false positives like a reliability problem with weekly ops review, not a one-off support headache. Track a small set of metrics: time-to-first-response for flagged candidates, time-to-clear, percent auto-cleared vs manually reviewed, and appeal overturn rate. If you need a starting target, set an illustrative goal like "clear benign flags within 1 business day," then tighten once you see volumes and staffing. When you see spikes, do not only tune thresholds. Look for root causes like webcam compatibility, VPN-heavy geographies, or assessment instructions that cause normal behavior to look suspicious.
Reason codes for every clearance and denial
A "complete packet" gate before manual review starts
Sampling audits of cleared cases to detect systematic misses
Sources
Key takeaways
- Treat fraud flags as risk signals, not verdicts, and require a second-source check before adverse action.
- Define ownership, SLAs, and sources of truth so Support does not become the decision-maker of record.
- Use Risk-Tiered Verification to step up only when needed, and to de-escalate quickly when evidence clears the candidate.
- Package every decision into an Evidence Pack so escalations end with facts, not opinions.
- Measure false positives as a support cost driver: ticket volume, time-to-clear, and candidate drop-off after review.
Operator-focused routing rules for flags from identity verification, AI interviews, and coding assessments.
Designed to minimize candidate friction while preventing silent overrides and preserving an Evidence Pack for every decision.
policy:
name: false-positive-triage-v1
owner:
business: recruiting-ops
security: ciso-office
support: candidate-support
sla:
first_response_minutes: 60
clear_or_stepup_hours: 24
decision_principles:
- "No adverse action on a single weak signal"
- "Two independent signals required for denial"
- "Lightest step-up first"
evidence_pack_required_fields:
- ats_candidate_id
- job_id
- event_timeline
- identity_verification_summary
- liveness_result
- device_and_network_summary
- assessment_telemetry_summary
- reviewer_notes
- decision_reason_code
routing_rules:
- id: env-only-benign
if:
all:
- flag.category == "environment"
- identity.verification_status == "passed"
- assessment.telemetry.prohibited_tool_signal == false
then:
action: "auto-clear"
ats_status: "assessment-cleared"
reason_code: "BENIGN_ENVIRONMENT"
notify:
- recruiting
- id: ambiguous-session
if:
any:
- assessment.telemetry.window_focus_loss_burst == true
- interview.voiceprint_conflict == true
then:
action: "step-up"
step_up:
type: "reverify-before-next-stage"
max_duration_minutes: 3
ats_status: "step-up-requested"
owner_queue: "support-intake"
reason_code: "SESSION_AMBIGUOUS"
- id: high-risk-identity
if:
any:
- identity.liveness_status == "uncertain"
- identity.face_match == "failed"
- identity.document_authenticity == "failed"
then:
action: "manual-review"
ats_status: "security-review"
owner_queue: "security-escalations"
require_dual_approval_for_denial: true
reason_code: "IDENTITY_RISK"
appeal_flow:
entrypoints:
- "candidate-support-portal"
- "recruiter-escalation"
allowed_requests:
- "re-run verification"
- "accessibility accommodation"
- "request decision explanation"
retention:
evidence_pack_days: 30
biometrics: "zero-retention-by-default"
audit_logging:
immutable_events: true
fields:
- actor
- timestamp
- action
- candidate_id
- evidence_pack_id
- previous_status
- new_status
integrations:
webhooks:
idempotency_key: "event_id"
retries: 5
backoff_seconds: 30
Outcome proof: What changes
Before
Flagged candidates were handled in ad hoc email threads. Recruiters pushed for overrides, Support had no consistent scripts, and Security only got involved after escalations went public.
After
Support runs a standardized intake with a 2-lane queue (auto-clear vs review), Recruiting Ops owns policy changes, and Security receives only high-risk identity cases with complete Evidence Packs.
Implementation checklist
- Create a two-lane queue: auto-clear vs manual review with explicit entry criteria.
- Publish a candidate-facing appeal path with a 1 business day response target (illustrative) and a human contact option.
- Define "adverse action" triggers and require two independent signals before denial.
- Standardize reviewer notes and required artifacts (doc match, liveness, device signals, assessment telemetry).
- Instrument outcomes: cleared, stepped-up, denied, withdrawn, and time-in-queue.
Questions we hear from teams
- What should Support do first when a candidate says they were falsely flagged?
- Acknowledge the issue, confirm you are reviewing, and immediately assemble the Evidence Pack (verification summary, telemetry, timeline). Do not label it as cheating, and do not promise clearance before review criteria are met.
- When is it appropriate to auto-clear a flag?
- Auto-clear when identity verification is passed and the flag is limited to common benign environment factors, with no corroborating assessment or interview anomaly signals. Record a reason code and keep the evidence summary.
- How do you avoid turning Support into the hiring decision-maker?
- Make Recruiting Ops the policy owner, require dual approval for denial in identity-risk cases, and limit Support to routing, evidence completeness, and candidate communication with SLAs.
- Do false positives mean your fraud detection is bad?
- Not necessarily. Some false positives are expected when you are catching rare but high-impact events. The problem is unmanaged false positives: unclear criteria, no de-escalation path, and inconsistent communication.
Ready to secure your hiring pipeline?
Let IntegrityLens help you verify identity, stop proxy interviews, and standardize screening from first touch to final offer.
Watch IntegrityLens in action
See how IntegrityLens verifies identity, detects proxy interviewing, and standardizes screening with AI interviews and coding assessments.
